HI there ! Today i upgrade my home lab to Ubuntu 22.04. It was a bit painful so i’ll share you some tips to help you 😉
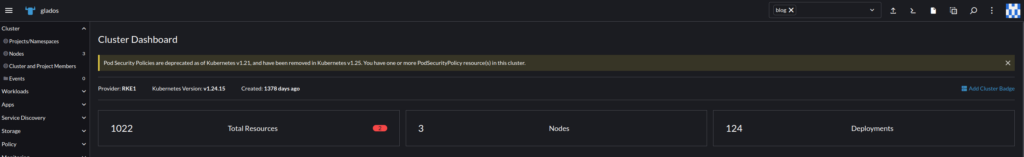
Disclaimers : I know RKE 1 is old, but for very tiny clusters it’s very handy. I just need to prepare SSH on all nodes ang go ! Moreover, my k8s cluster is now 5 years old, and migration from RKE1 to RKE2 is too complicated for little benefit…
Ok now, here we go !
RKE 1 requirements
Use iptable instead of nftable
RKE1 need to use iptable instead of nftable.
echo 'net.bridge.bridge-nf-call-iptables=1' | sudo tee -a /etc/sysctl.conf sysctl -p
Use containerd instead of dockershim
You can make new out of old with RKE 1 and use containerd instead of dockershim. This modification is mandatory for using some project on your k8s cluster, for example, Gitpod : https://github.com/gitpod-io/gitpod/issues/5410
- First, on each nodes, enable CRI plugin by modifying
/etc/containerd/config.toml
disabled_plugins = []
- Run
systemctl restart containerd - Modify
kubeletsection in your RKE configuration file to use containerd instead of dockershim
kubelet:
extra_args:
container-runtime: remote
container-runtime-endpoint: 'unix:///run/containerd/containerd.sock'
extra_binds:
- '/var/lib/containerd:/var/lib/containerd'Enable systemdCgroup in containerd
One of my old issue was about RKE1 compatibility with Ubuntu 22.04.
We need to enable SystemdCgroup in containerd daemon because it cause kube-proxy configuration reload…
Thanks to @jroose on Github, we have a workaround :
mkdir -p /etc/containerd containerd config default > /etc/containerd/config.toml # Reverts the containerd config to the default configuration sed -i 's/SystemdCgroup = false/SystemdCgroup = true/g' /etc/containerd/config.toml systemctl restart containerd